Events
This site contains all relevant Events by ABC4trust. To keep you updated, we have a RSS Feed with ABC4Trust Events.
On January 20, 2015 ABC4Trust presented the results of four years of intense research and piloting of privacy-enhancing authentication solutions in a full-day event. The meeting took place right in the heart of the European Quarter in Brussels at the new venue of the Representation of the State of Hessen to the EU,
The meeting took place right in the heart of the European Quarter in Brussels at the new venue of the Representation of the State of Hessen to the EU,
21 Rue Montoyer, Brussels.
The date conveniently allowed interested privacy experts to attend the
Summit Event in connection with their travel to attend the Computers,
Privacy and Data Protection Conference 2015 (CPDP) which takes place Wednesday 21 until Friday 23 January, 2015 at Les Halles de Schaerbeek in Brussels, Belgium.
| Agenda | ||
| 08:45 | Registration and Coffee | |
| 09:30 | Opening & Welcome Jochen Marsch (Representation of the State of Hessen to the EU) Prof. Dr. Birgitta Wolff (President of Goethe University Frankfurt) |
|
| "EU funded research is keeping up trust in digital society" Rafael Tesoro Carretero (European Commission - Directorate-General for Communications Networks, Content and Technology - Trust and Security) |
||
| "Privacy-respecting Identity Management Introduction to ABC4Trust" Prof. Dr. Kai Rannenberg (Goethe University Frankfurt) |
||
| 10:30 | The Patras Pilot: | “ePolls and evaluations” Prof. Dr. Yannis Stamatiou (Computer Technology Institute & Press - DIOPHANTUS) |
| "Architecture: Mandatory roles and features" Ahmad Sabouri (Goethe University Frankfurt) |
||
| Demo Prof. Dr. Yannis Stamatiou (Computer Technology Institute & Press - DIOPHANTUS) |
||
| 11:20 | Coffee Break | |
| 11:50 | The Söderhamn Pilot: | “Community interaction platform” Souheil Bcheri (Eurodocs AB) |
| "Architecture: Optional roles and further features" Ahmad Sabouri (Goethe University Frankfurt) |
||
| Demo Souheil Bcheri (Eurodocs AB) |
||
| 12:40 | "Architecture layers" Ahmad Sabouri (Goethe University Frankfurt) |
|
| 13:00 | Lunch break | |
| 14:00 | Greeting Address from the European Parliament Jan Philipp Albrecht (MEP, Greens/EFA, EP Rapporteur General Data Protection Regulation) |
|
| 14:15 | “NSTIC at 4: Putting an ecosystem into operation” Michael Garcia (Deputy Director National Strategy for Trusted Identities in Cyberspace, National Institute of Standards and Technology, U.S. Department of Commerce - NIST) |
|
| 15:00 | "The ABC4Trust Reference Implementation" Dr. Michael Østergaard (Miracle A/S) |
|
| 15:25 | "ABC4Trust on Smart Cards" Dr. Pascal Paillier |
|
| 15:45 | "Privacy-ABC Technology on Mobile Phones" Gert Læssøe Mikkelsen (Alexandra A/S) |
|
| 16:05 | "A Movie Streaming Application & ABC4Trust as Services on the Cloud" Dr. Anja Lehmann (IBM Research Zurich) |
|
| 16:25 | Coffee Break | |
| 16:45 | Panel discussion: | “Global and European Identity Initiatives (and ABC4Trust)” |
| Chair: Marit Hansen (Deputy Chief of the Independent Centre for Privacy Protection Schleswig-Holstein, ULD) |
||
| Panellists: - Ronny Bjones (Microsoft), - Neil Clowes (EC - eIDAS Task Force), - Robert Seidl (Nokia), - Achim Klabunde (EDPS), - Kai Rannenberg (Goethe University Frankfurt) |
||
| Greeting Mark Weinmeister (State Secretary of European Affairs at the Hessian State Chancellery) |
||
| 18:15 | Reception; introducing the “ABC4Trusters” | |
If you like to be notified about news on the ABC4Trust Summit Event please let us know at:

Please also note the agenda of the upcoming Computers, Privacy and Data Protection conference 2015 which will be held in Brussels 21st - 23rd of January, 2015.
ABC4Trust Information Event in Athens
The ABC4Trust project invited interested people from industry, politics and science to join its information event held in Athens. The project's partners introduced the audience to Privacy-ABCs technologies in general, the architecture and the project's pilots. The presentation slides are available as PDF download (see below).
Date:
September 29, 2014, starting at 10:00h
Venue:
CTI building
Mitropoleos 26-28,
105 63 Athens
Programme
|
Time |
Speaker |
Subject |
|
10:00-10:30 h |
|
Registration and Welcome Coffee |
|
10:30-11:00 h |
Tasos Economou (Kathimerini) |
Keynote: "Digital privacy: A journalistic perspective" |
|
11:00-11:30 h |
Prof. Kai Rannenberg (GUF) |
Introduction to the ABC4Trust Project and Privacy-ABCs Download PDF |
|
11:30-13:00 h |
Souheil Bcheri (EDOCS)
Prof. Yannis Stamatiou (CTI) |
Privacy-preserving School Communication for Pupils, The Söderhamn Pilot Download PDF Anonymous Course Evaluations at Universities; The Patras University Pilot Download PDF
|
|
13:00-14:00 h |
|
Light lunch; demonstrators available on desk; FI-Ware demo by NSN Download PDF |
|
14:00-14:25 h |
Ahmad Sabouri (GUF) |
ABC4Trust Architecture Download PDF |
|
14:25-14:50 h |
Dr. Michael Østergaard (MCL) |
ABC4Trust Reference Implementation Download PDF |
|
14:50-15:15 h |
Pascal Paillier (CRX) |
Smart Card Implementation (Including live demo) |
|
15:15-15:40 h |
|
Coffee Break |
|
15:40-16:05 h |
Dr. Gert Læssøe Mikkelsen (ALX) |
Privacy-ABC technology on Mobile Phones Download PDF |
|
16:05-16:30 h |
Dr. Jan Camenisch (IBM) |
ABC4Trust as Services in the Cloud |
|
16:30-17:00 h |
Prof. Kai Rannenberg; Prof. Yannis Stamatiou |
Discussion and Conclusions |
Read more: September 29, 2014 - ABC4Trust Information Event in Athens
The 9th international IFIP summer school on privacy and identity management for the future internet in the age of globalisation took place on September 7-12, 2014 in Patras, Greece.
This year's summer school was hosted by ABC4Trust consortium partner CTI - Computer Technology Institute and Press "Diophantus" located near the University of Patras.
This annual event is organised by the IFIP working groups 9.2, 9.5, 9.6/11.7, 11.4, 11.6 and special interest group 9.2.2. ABC4Trust co-organizes the joint effort of several research projects to keep the IFIP summer school series up. For the event in 2014 summer school was hosted by our Greek ABC4Trust partner CTI with Yannis Stamatiou as organizing committee chair. Further ABC4Trust involvement consisted of Marit Hansen (ULD) as general chair and Jan Camenisch (IBM) as a program committee co-chair.
The IFIP summer school 2014 was interactive in character, and composed of keynote lectures and workshops with master/PhD student presentations. The principle is to bring together junior and senior researchers and practitioners from multiple disciplines to discuss important questions concerning privacy and identity management and related issues in a global environment. To this end, contributions from students at the stage of preparing either a master’s or a PhD thesis are especially encouraged.
ABC4Trust was represented by two keynote speakers and an afternoon workshop, providing three parallel sessions. Furthermore, the project was addressed in several student papers.
Participants of the IFIP Summer School 2014 can view all slides of the ABC4Trust sessions here.
Important Dates
| Event | Deadline |
|---|---|
| Final paper for Springer proceedings | 28 November 2014 |
| Notification of acceptance of the final paper | 30 January 2015 |
| Camera ready for proceedings | 28 February 2015 |
General Chair: Marit Hansen
PC Co-Chairs: Jan Camenisch, Simone Fischer-Hübner, Ronald Leenes
Organizing Committee Chair: Yannis Stamatiou
July 17, 2014 - ABC4Trust at the Greek Ministry of Foreign Affairs
After the successful operation of the Patras pilot, ABC4Trust was invited (through the University of Patras Innovation Office) to present its results at a one-day event organized by the Greek Ministry of Foreign Affairs (MFA).
The event will take place on July 17, 2014, at the amphitheatre “Kranidiotis” of the MFA at Akadimias 1 Str., Athens, Greece.
The goal of the event is to promote mature research results (which are ranked above 6 at the Technology Readiness Levels) to interested parties, who might include the immediate exploitation in their business plans.
Invitations were sent to ambassadors and finance/commerce State representatives of foreign countries, as well as to their Greek counterparts. Also, invitations were sent to representatives from the private and public sector in Greece.
ABC4Trust Workshop at the Cyber Security & Privacy Forum 2014 in Athens
ABC4Trust organised a workshop at this year’s CSP Forum Conference, held in Athens, Greece. The workshop ‘ABC4Trust – Putting Privacy-ABCs into Practice’ consisted of two parts. (‘Track 12’ and ‘Track 15’ on the conference programme.)
All presentations can be found here.
Speakers:
Gregory Neven (IBM) - The Concept of Privacy-ABCs
Jonas Lindstrøm Jensen (Alexandra Institute) - Privacy-ABCs on Mobile Devices
Souheil Bcheri (Eurodocs AB) - Community Interaction Among Pupils
Yannis Stamatiou (Diophantus) - Privacy Preserving Course Evaluation in Educational Institutes
Ahmad Sabouri (Goethe University Frankfurt/Main) - Enabling Privacy Friendly Integration of Cloud Services into Enterprises
Chair: Hannah Obersteller (ULD)
In the first part, Gregory Neven introduced the audience to the idea and the functionalities of Privacy-enhancing Attribute-based Credentials (Privacy-ABCs). After describing existing identification schemes and their weaknesses, Dr. Neven explained the advantages of Privacy-ABCs. Privacy-ABCs allow the user to choose which information – in other words: which attribute – he is willing to reveal. In the following, he focused on the more advanced features such as pseudonyms, revocation, and inspection. While by default Privacy-ABCs allow the user to access a service completely anonymously, the optional feature “inspection” can be enabled if needed. This means, the identity of the user can be revealed conditionally. The user must be informed in advance if inspection is enabled and under which circumstances (inspection grounds) his identity may be revealed. The revocation feature allows the issuer of the credentials to revoke them. This might become necessary if a certain attribute of the user changes; e.g. if he is not a student anymore.
Jonas Lindstrøm Jensen showed examples of how Privacy-ABCs can be used on mobile devices. While the project’s trials were using laptops as devices, it is also possible to use mobile devices like mobile phones or tablets. The advantage is, that most potential users already have one, so there is no need for additional hard ware like smart cards and smart card readers. Mr. Lindstrøm Jensen referred to new use cases and the security and privacy problems that, in turn, appear.
Souheil Bcheri presented the results of one of ABC4Trust’s trials. ABC4Trust set up a School Communication System at a Secondary School in Söderhamn/Sweden. Functionalities like chat and document sharing are provided as well as counselling sessions and political discussions. The pupils, their parents and teachers are enabled to access the network pseudonymously or anonymously, depending on the service they want to use. Since there had not been a similar application before, ABC4Trust had to create it from sketch. The network offers certain “rooms” – Restricted Areas – to certain group of users. Depending on the individual access policy of each of those Restricted Areas, there can be e.g. a chat room that allows access for everyone who can prove that she is not elder than 14 and a girl. The users can create own Restricted Areas and determine their access policies as well.
Building on what had been presented in the first part, in the second part Yannis Stamatiou reported on the results of the second trial of ABC4Trust, also by showing screenshots and video sequences. The project implemented a Course Evaluation System at the University of Patras, Greece. The students are enabled to evaluate their Courses anonymously. At the same time the system guarantees that only duly accredited students can participate in the evaluation. As an incentive to the students to participate in the trial, the students could choose to get another credential. This so-called Tombola credential allowed them to participate in a Tombola at the end of the semester. The inspection feature was used to reveal the identity of the winner. All other credentials were not inspected. The revocation feature was employed to allow the university to revoke a student’s credential when he leaves the university. After the explanation of the system, Prof. Stamatiou talked about the results of an anonymous questionnaire that was answered by the students who participated in the trial. According to the evaluation the students understood the functionality and also trusted the system. Prof. Stamatiou also reported on the future exploitation of the system.
Finally, Ahmad Sabouri gave a presentation on a special future use case of Privacy-ABCs: Use on the Cloud. After giving an introduction to Cloud Services in general, he talked about what might keep enterprises from using them. One major issue is privacy and identity concerns. Identity management in the cloud is different. Mr. Sabouri described the Privacy requirements in the Cloud. While the IdMaaS must not learn about the services the user accesses, the Cloud Provider may be neither able to link a user to his identity, nor to profile the user based on his different accesses. Furthermore, the Cloud Service Provider should not learn about the use of resources and services, while the enterprises should be able to audit those. Then, he explained in how far Privacy-ABCs meet those requirements and mapped the roles of the entities of a Privacy-ABC system.
Questions were answered during and after each presentation.
ABC4Trust Workshop at the Trust in Digital Life Trust Event 2014 in Vienna
The annual Trust in Digital Life event took place on April 7th and 8th, 2014 in Vienna.
The ABC4Trust Project organized Track 3 “Identity management” and offered a panel featuring a variety of current applications of Privacy-ABC. The workshop targeted everyone that wants to implement privacy-preserving identity management. The panel demonstrated that usable and trustworthy identity management systems are technically possible and in several cases already a working reality. In the track the following presentations were covered:
General technology presentation of ABCs in ABC4Trust
(Dr. Gregory Neven, IBM)
Privacy respecting ICT innovations in education: electronic course evaluations in higher education and beyond
(Prof. Yannis Stamatiou, Computer Technology Institute and Press)
Restrictive download of documents from cloud storage in FI-Ware
(Robert Seidl, Nokia Solutions and Networks)
Performance of privacy-enhancing cryptography on smartphones
(Dr. Jan Hajny, Brno University of Technology)
Information security supporting data protection
(Dr. Rodica Tirtea, ENISA)
Major questions and discussions in the panel:
- What would be some interesting examples of Privacy-ABCs applications?
Apart from the pilots of ABC4Trust that deal with privacy-friendly online course evaluation and privacy-friendly school community platform, one could consider e-government polls, age verification and public transportation ticketing to be very relevant problems that can be addressed using Privacy-ABCs.
- There are so many cryptographic solutions to deal with privacy problems. Why to use ABC4Trust framework and not any other one?
ABC4Trust framework is defined in a generic way based on the identified features that are required from Privacy-ABCs. Therefore it gives the opportunity to any crypto provider to implement the specified interfaces and therefore be pluggable to the framework. ABC4Trust is not limited to any specific technology and it also helps to avoid a lock-in situation.
- One of the major blocking factors in front of adoption of Privacy-ABCs concerns the application developers not being familiar with the crypto. What can be done in this regard?
The ABC4Trust project has provided a crypto-agnostic API set to Privacy-ACBs, which relieves the burden of complicated crypto. The reference implementation of ABC4Trust is publicly available on Github along with documentations and integration examples for the developers.
- How is it possible to convey the properties of Privacy-ABCs to the end users?
Indeed a certain level of trust is needed for the ecosystem to work. Trust in the crypto, trust in the correct implementation of the crypto and trust in the correct deployment of the system are the minimum requirements. Perhaps there should be some consumer protection or verification agencies to help with gaining the trust of the end users in the system and the promised features.
February 28, 2014 ABC4Trust at EU Cybersecurity Strategy - High Level Conference in Brussels
Brussels, February, 28th, 2014: The ABC4Trust project is present at the "EU Cybersecurity Strategy - High Level Conference" with a booth and strong presence of the ABC4Trust members. The one-day Conference is organised by the European Commission, in cooperation with the European External Action Service.
Keynotes have been provided by Ms Neelie Kroes, Commission Vice-President for the Digital Agenda and Mr Maciej Popowski, Deputy Secretary General of the European External Action Service.
In her keynote Ms Neelie Kroes stated that in the field of cybersecurity we in Europe need to say “yes” to data protection and “no” to data protectionism. We also should not get too entangled in viewing ongoing revelations by Edward Snowden but recognize that cybersecurity is also about the aspects directly relevant for the citizens: People trusting that their personal data on social network sites are well protected; users understanding what their cloud service providers are offering, eID solutions allowing to securely authenticate towards services; or children’s sufficiently protected but also empowered to avoid online risks.
ABC4Trust addresses many of the aspects mentioned in the vice president’s keynote. The Swedish Pilot provides a school network for information exchange at a school where pupils are empowered to communicate securely within verified areas while retaining their anonymity to the extent possible or acting under pseudonyms. Data protection and data minimisation is a core feature built into Privacy-enhanced Attribute-based Credentials (Privacy-ABCs) – presumed that the systems are set up accordingly. The data minimisation principle states that (only) the data necessary for a given and defined purpose may be processed. Privacy-ABCs permit to remove data from a certificate that are unnecessary while retaining the integrity of the issuer’s signature for the remaining information.
At the High Level Conference on the EU Cybersecurity Strategy ABC4Trust is present with a booth where both ABC4Trust pilots are on display. Prof. Kai Rannenberg from  Goethe University Frankfurt, Germany, is project lead of the ABC4Trust project. The Swedish school pilot is presented by Souheil Bcheri of Eurodocs. Prof. Yannis Stamatiou from The Computer Technology Institute & Press – Diophantus, Greece, shows the university pilot allowing anonymous evaluation of lectures. Harald Zwingelberg from the Unabhängigen Landeszentrum für Datenschutz, Germany, presents comments on legal aspects of Privacy-ABCs to support eID solutions across Europe.
Goethe University Frankfurt, Germany, is project lead of the ABC4Trust project. The Swedish school pilot is presented by Souheil Bcheri of Eurodocs. Prof. Yannis Stamatiou from The Computer Technology Institute & Press – Diophantus, Greece, shows the university pilot allowing anonymous evaluation of lectures. Harald Zwingelberg from the Unabhängigen Landeszentrum für Datenschutz, Germany, presents comments on legal aspects of Privacy-ABCs to support eID solutions across Europe.
Keynote Speaker Dr. Thomas Kremer, Member of Deutsche Telekom’s Board of Management for Data Privacy, Legal Affairs and Compliance, showing great interest in the ABC4Trust pilot systems
November 13, 2013 IDManagement workshop in Copenhagen
 On November 13th 2013, ABC4Trust partner Alexandra Instituttet co-organised a workshop entitled 'ID management' together with with DI ITEK in Copenhagen, Denmark.
On November 13th 2013, ABC4Trust partner Alexandra Instituttet co-organised a workshop entitled 'ID management' together with with DI ITEK in Copenhagen, Denmark.
Five international experts provided insights on identity related topics such as the internoperationality of national eID solutions, open standards in the field secure management of identities on mobile devices. The event was targeted at IT architects, decision-makers and developers in the field of online services and cloud solutions and fully booked.
The program featured the following presentations:
- Digital authentification solutions, both in general and in relation to NemLogin, Thomas Gundel, IT Crew
- Interoperability among national e-ID infrastructures, Gunnar Nordseth, CEO, Signicat
- International open standards, including OpenID connect and OAuth2, Justin Richer, MITRE
- MS U-Prove and identity management in the cloud, Ronny Bjones
- Secure identity management on mobile devices, Stefan Hebsgaard, Cryptomathic
November 13, 2013 Third ABC4Trust Reference Group Meeting
The third Meeting of the ABC4Trust Reference Group is going to happen on November 13th and 14th, 2013 in Frankfurt, Germany. The Reference Group is a board of selected experts from the relevant stakeholders from inter alia ICT industry, academia, specialized press, data protection authorities, and civil society groups.
The ABC4Trust Reference Group is designed to provide early feedback on the ABC4Trust Project results from different viewpoints, considering the overall value and potential use of the ABC4Trust Project results. As such, it will provide global, non-technical advice to the ABC4Trust Project, focusing on its scientific direction and its prospects for exploitation and research in the mid and longterms. Together with the participants of ABC4Trust, the ABC4Trust Reference Group prepares the transfer of its results to industry and standardisation organisations to support European privacy regulations.
November 8, 2013: ABC4Trust chairing the ACM Digital Identity Management Workshop 2013 at ACM CCS 2013
ABC4Trust will be jointly chairing the ACM Digital Identity Management Workshop 2013 together with the FutureID project at the annual Conference on Computer and Communications Security (CCS) of the Special Interest Group on Security, Audit and Control (SIGSAC) of the Association for Computing Machinery (ACM). The conference will be held in Berlin from November 4th -8th and is a high profile research conference in the area of cyber security.
The workshop on Digital Identity Management is chaired by Thomas Groß and Marit Hansen of the FutureID and ABC4Trust projects. In five sessions the workshop will explore the central issues in connection with interoperable identity management technologies in the information society:
Session 1: Welcome and Keynote by Claudia Diaz
Session 2: Cryptographic Methods
Session 3: Human Factors and Socio-Economic Aspects
Session 4: Security Considerations
Session 5: eIDs and Identity Management
For further information please refer to the detailed workshop program.
July 10, 2013: Futurium Webinar on Privacy and the Draft eIDAS Regulation
Futurium webinar on Impact of the draft eIDAS Regulation on privacy preserving eID solutions

The draft eIDAS Regulation currently in discussion at the European Parliament will have a major impact on how trust and privacy can be preserved and managed in the future Internet and any related development in society. The impacts on privacy-preserving eID technologies will be content of a talk at a webinar by Harald Zwingelberg. The webinar is moderated by Jacques Bus (Digital Enlightenment Forum) and will held on July 10th, 2013 at 16:00 CET.
Prior to the ABC4Trust introduction Ms Carolyn Nguyen (Microsoft, US) will give a new stimulus to the discussion on personal data ecosystems.
For the detailed agenda of the Webinar and the details how to listen or participate in the online discussion please visit the Futurium website.
For further details on the eIDAS regulation under a privacy specific viewpoint see can be found here.
July 8, 2013: ABC4Trust present at the SIIIC conference
The ABC4Trust project will be present at the "SSEDIC International Identity Initiatives Conference" (SIIIC) in Rome on July 8th, 2013. Harald Zwingelberg will introduce the audience of experts in the field of electronic identity devices to the ABC4Trust results and discuss how the draft eIDAS regulation could be altered to pave the way for user-centric and privacy-enhancing eID solutions in Europe.
For details on the SIIIC conference please refer to the SIIIC website.
ABC4Trust at TDL and CSP 2013
ABC4Trust will be present at the joint event of the Cyber Security Privacy EU Forum 2013 and Trust in the Digital World 2013 in Brussels, April 18th-19th, 2013.
ABC4Trust involvement
- ABC4Trust session, Thursday, April, 18th, 16:15.
- Presentation “Privacy-Enhancing Attribute-Based Credentials and eIDs: Chances, technical Possibilities and legal Prerequisites” as be part of the session security and Privacy Services in The Horizon”, Friday, April 19th, 14:00.
- Demonstration of the ABC4Trust university pilot in the demonstration area.
The ABC4Trust session
In June 2012 the EU Commission adopted a proposal for a “Regulation of the European Parliament and the Council on electronic identification and trust services for electronic transactions in the internal market” (COM/2012/238/FINAL, hereinafter eIDAS Regulation). The eIDAS Regulation aims to bring trust to electronic transactions in the European market by inter alia providing for a mutual recognition and acceptance of national eID solutions. To have its national eID solution recognized and accepted in other Member States the Member State of origin may notify its national eID solution to the commission. Provided a series of requirements are fulfilled such notified schemas must be recognized EU wide. At present, the draft eIDAS Regulation is open for discussion and comments in the European parliament. A session with expert input and discussions with the high level audience may positively influence the decisions on details of the Regulation. The eIDAS Regulation causes concerns that it may hinder or even block the further development of privacy-enhancing solutions in the field of electronic Identifiers (eIDs). Some of these aspects have been pointed out in the ABC4Trust position paper on the eIDAS Regulation.
The ABC4trust session on Thursday will focus on the potential of privacy-enhancing attribute-based credentials (Privacy-ABCs) in the field of eIDs. For this part, we will start with a quick introduction to the privacy-enhancing features of the solution, and to the ABC4Trust project as a whole followed by a more detailed description of the ABC4Trust architecture. Two different approaches for integrating Privacy-ABCs with eID systems will be discussed, and elaborated on the benefits of Privacy-ABCs when building privacy-respecting eID systems. ABC4Trust’s Greek university pilot where smartcards are deployed for a secure and anonymous authentication towards a system for evaluating lectures – deployable e.g. for online participation of citizens in local decisions, polls, or surveys is presented next. Finally a data protection-oriented view on the draft eIDAS Regulation will be provided, elaborating on how Privacy-ABCs could enhance future eIDs, showing which adaptations might be necessary to the current draft eIDAS Regulation in order to allow and support such adaptations. The last talk is intended to encourage an open discussion with the participants on these particular topics of the eIDAS Regulation.
The ABC4Trust project and privacy-enhancing Attribute-based Credentials – enabling data protection features for future electronic authentication, by Prof. Kai Rannenenberg,
The first talk will introduce the ABC4Trust project before central principles and functionalities of Privacy-ABCs will be described. The audience will learn how anonymous authentication can be performed trustworthy and securely bound to one person, e.g. the holder of an eID token, by deploying cryptographic mechanisms. Further, necessary features such as an issuance, presentation, and revocation of credentials will be discussed. Provided the user submitted her identity information in an encrypted container at time of authentication, the optional inspection feature allows to later identify an otherwise anonymous user under previously fixed conditions, e.g. if that user violated applicable laws.
The ABC4Trust Architecture – making Privacy-ABCs deployable and interoperable, by Dr. Ioannis Krontiris
The goal of the presentation is to show that Privacy-ABCs have become an attractive solution to offer privacy in eID systems. In particular, we will report on the progress being made within the ABC4Trust project in terms of bringing together different Privacy-ABC technologies and building a unified architecture for their interoperation.

Figure: A high level view of the ABC4Trust Architecture
Then, we will discuss some of the privacy and security threats that exist in today’s eID systems, and elaborate on the advantages of using Privacy-ABCs to address these threats. Following that, we will discuss two approaches for integrating Privacy-ABCs with eID systems, taking the German eID system as a case study. In the first approach, we show that by introducing a new entity in the current German eID system, the citizen can get a lot of the Privacy-ABCs advantages without further modifications. Then, we will concentrate on the possibility of putting Privacy-ABCs directly on smart cards, and we will present new results on performance, which demonstrate that it is now feasible for smart cards to support the required computations these mechanisms require.
Anonymous authentication for polls and surveys with Privacy ABCs – The ABC4Trust university pilot leading the path to more eID features for citizen eParticipation?, by Prof. Yannis Stamatiou
The presentation on the ABC4Trust university pilot is intends to show the results of one of the two pilots in ABC4Trust. The ABC4Trust project addresses the federation and “interchangeability” of technologies that support Privacy-ABCs. For this pilot, the participating students collect a series of credentials to verify that they are eligible to anonymously participate in an evaluation of the quality of a lecture. The pilot, whose operation may be presented during a demo at the CSP EU Forum, comprises the provision of credentials to the students of a Greek university that certifies, using Privacy-ABCs, a number of facts of the students (e.g. registered courses, class attendance information, etc.). Eligible Students will be able to anonymously provide feedback on courses and teachers they had during a semester by using proper credentials stored on their smart cards. The attribute selection feature here allows students to verify information such as their participation in a course, without giving away their name or matriculation number stored on the same eID token. The pilot thus also provides a good test bed for other types of polls, petitions, and other means of opinion making. Such features may be interesting to support for national eIDs enabling citizens to easily participate in local politics, petitions, or other means of direct democracy in governmental and private organisations.
The draft eIDAS Regulation and its impact on privacy preserving technologies in the field, namely Privacy-enhancing Attribute-based Credentials, by Harald Zwingelberg
The legal and policy oriented presentation on the draft eIDAS Regulation will summarize the currently foreseen framework described in chapter two of the draft eIDAS Regulation. European eID experts share the opinion that upcoming eID schemas should support data minimisation by allowing attribute selection and that pseudonymous or anonymous authentication should be possible and enforced on relying parties where necessary (see SSEDIC eID Adoption Survey p. 32 et seq.). However, the current draft of the eIDAS Regulation does not foresee data minimisation, nor does it require foreign services to adhere to the principle of data minimisation even if the national eID of the customer supports such features. Here, further development in the area of eIDs should not be hindered but rather encouraged, in order to raise hope that future versions of eIDs may support privacy enhancing solutions such as Privacy-ABCs or the already existing solution of the German national eID “neuer Personalausweis”.
Further, the national authentication service, which is mandatory for all notified eID schemas, is likely to be able to profile the behavior of the users by learning which services from outside of the own member state have been visited by the users. For the authentication services, but also for any other involved entities, clear data protection rules including maximum retention periods for personal data are necessary, and need to be incorporated in the eIDAS Regulation. This presentation will provide some potential solutions as basis for further discussion with the audience.
See also the ABC4Trust web-page dedicated to the eIDAS Regulation here.
Sep. 5, 2012: ABC4Trust at Trustbus'12
The ABC4Trust Project will be presented at the 9th International Conference on Trust, Privacy & Security in Digital Business (TrustBus 2012), which will take place in Vienna, 4-6 September 2012. A special session has been organized on research conducted within European FP7 projects related to Trust, Privacy and Security on Wednesday afternoon, 5th September. In this special session, ABC4Trust will present its main research challenges & results in a short presentation and with a poster, which will be exhibited in or near the conference room. A two pager introducing ABC4Trust project will be published in the TrustBus 2012 conference proceedings by Springer LNCS.
Events
This site contains all relevant Events by ABC4trust. To keep you updated, we have a RSS Feed with ABC4Trust Events.
Privacy-ABCs to be demonstrated at eID Conference in Biel,May 27th-28th 2012
At the European eID Interoperability Concepts and Compliance Conference, ABC4Trust partner IBM Research will be present with a demonstration on Privacy-Preserving Authentication by Attribute-based Credentials. The conference will take place in Biel, Switzerland from May 27th-28th, 2012.
Authentication is an all-embracing mechanism in today’s digital society. Current authentication systems require users to provide more personal data than actually necessary, and offer many attack vectors due to insecure authentication methods such as username/passwords. With Privacy-preserving Attribute-based Credentials, systems that allow for minimizing the data released during authentication do exist. A combination of these technologies with eID solutions could provide the necessary security and trust for all participants while preserving the user’s privacy at the same time. In the current discussion for future electronic IDcards and other means to authenticate online and offline, the growing privacy threats for users are not sufficiently reflected. Therefore, any upcoming European and national eID schemas should help citizens to protect their privacy by pr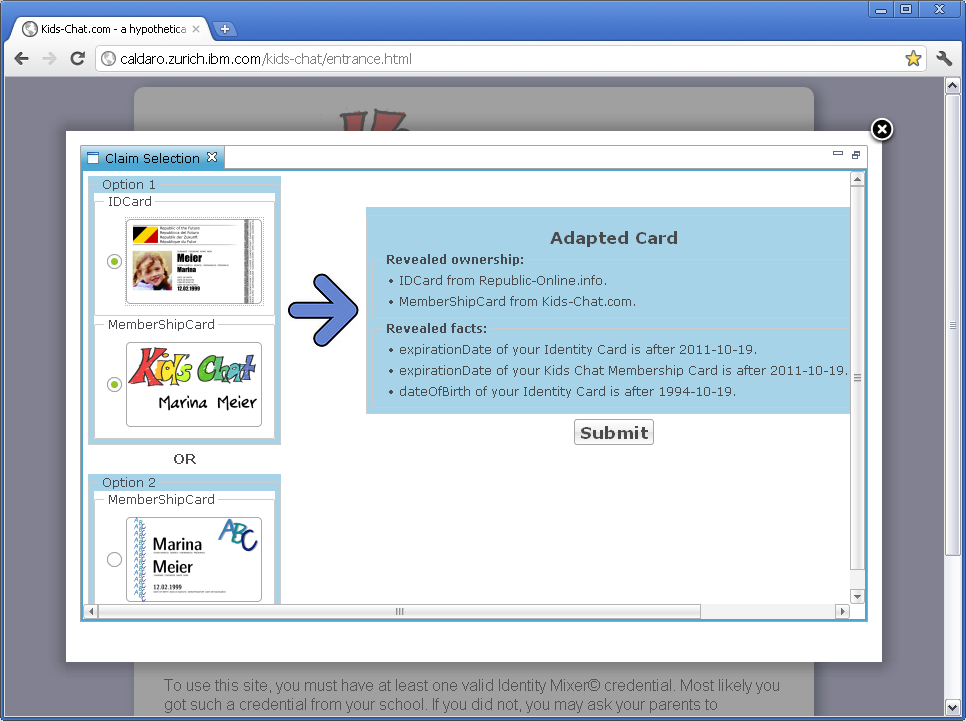 oviding secure authentication methods with which the user can verify only the relevant attributes but does not need to reveal more than these necessary attributes. Users would be enabled to act under a pseudonym with their real identity unknown to the service provider. However, acknowledging risks for service providers, it should be possible to trace back a so far pseudonymous user under certain previously specified conditions. With Privacy-preserving Attribute-based Credentials, such as IBM’s Identity mixer presented at the conference in Biel or Microsoft’s U-Prove, technology can be a key enabler for privacy preserving eID solutions in the future.
oviding secure authentication methods with which the user can verify only the relevant attributes but does not need to reveal more than these necessary attributes. Users would be enabled to act under a pseudonym with their real identity unknown to the service provider. However, acknowledging risks for service providers, it should be possible to trace back a so far pseudonymous user under certain previously specified conditions. With Privacy-preserving Attribute-based Credentials, such as IBM’s Identity mixer presented at the conference in Biel or Microsoft’s U-Prove, technology can be a key enabler for privacy preserving eID solutions in the future.
The demonstration in the conference’s exhibition area will show data-minimizing authentication with attribute-based credentials based on the scenario of a teenage chat room, where the chat provider requires authentication with respect to a service-specific privacy-preserving policy. When a user wants to enter the chat room, the implementation determines whether and how the user can fulfil the policy with her credentials. A graphical user interface allows the user to select and verify which personal information she wants to use to fulfil the policy. Prior to sending any information, the user interface also provides her with a detailed summary of which information she is about to release to the service provider. Based on the user's input, the prototype generates a cryptographic presentation token that shows fulfilment of the service provider's policy without revealing any unnecessary information. Finally, this presentation token is sent to the service provider for verification who grants access to the chat accordingly. Our prototype is the first implementation of such far reaching data-minimizing privacy-preserving authentication.
Visitors of the demo will learn that it is possible to perform online authentication in a privacy-preserving manner.
Resources:
-
For first information on Privacy-ABCs, the problems they can solve and what the project is about see the ABC4Trust Flyer.
-
For a description of the demo to be shown in Biel see Bichsel/Preiss, A Comprehensive Framework Enabling Data-Minimizing Authentication, 2011.
-
Read more on an architecture to make existing systems of Privacy-ABCs interoperable, and the how the processing of personal data can be limited to enhance privacy and legal compliance: D2.1 Architecture for Attribute-based Credential Technologies.
ABC4Trust Tutorial at CSP EU Forum, Berlin, April, 24th 2012
Privacy-Enhanced Credentials Going Live – From Theory to Practice, ABC4Trust tutorial at CSP EU Forum, Berlin April, 24th 2012
ABC4Trust will hold a tutorial session at the Cyber Security & Privacy EU Forum 2012 (CSP EU FORUM) under the title “Privacy-Enhanced Credentials Going Live – From Theory to Practice”. The tutorial will be part of the CSP EU Forum in Berlin, Germany, on April, 24th 2012.
[Update] The organizers published the agenda with the time slot for our tutorial. Join us on the first day of the conference (April 24th) between 16:00 and 18:00. Please note also that the CSP EU forum is now open for registration.
Trustworthy authentication and authorization is one of the main ingredients to ensure secure transactions over the Internet. The currently prevalent solution for user-authentication is by username and password. In case the authorization requires information about the user such as address or credential card number, these information are typically obtained by exchange with other service providers. Increasingly, cryptographic approaches such as X.509 certificates are used that offer stronger security guarantees. Both of these approaches have considerable privacy concerns. Briefly, the users have to reveal their full identity and personal data to one or more service providers even though that amount of information would not be strictly necessary.
In tutorial session the presenters will discuss how Privacy-ABCs can provide the same, or better, level of strong authentication while preserving the privacy of the user. In a nutshell, privacy-ABCs allow the user to establish several partial identities (1) with each service provider, where they only disclose the information that is minimally required for this purpose. For instance, it often might be sufficient to prove the mere fact that the user is over 18 instead of revealing the full date of birth.
The technology to deploy privacy attribute-based credentials is already available with IBM's Identity Mixer and Microsoft's U-Prove. Currently, both are being integrated and used for two pilots in the EU-funded project ABC4Trust project which takes up the heritage of the European PRIME and PrimeLife projects.
This tutorial aims at providing a better understanding of the features and concepts of Privacy-ABCs and its potential application areas. We will also discuss how the ABC4Trust project advances the current state by identifying a common architecture (2) and deploying Privacy-ABCs in real-life environments. Presentations of the two pilot scenarios and a legal assessment of such privacy-enhancing technologies will complete this tutorial.
Agenda of the Tutorial session
More precisely, the tutorial consist of the following three parts:
Read more: ABC4Trust Tutorial at CSP EU Forum, Berlin, April, 24th 2012
ABC4Trust Public Event in Athens, Greece
Attribute Based Credentials for privacy preserving identity management:
Legal and technical issues, implementation initiatives, and future trends
September 20th 2011, TITANIA HOTEL, Panepisthmiou 52 , Athens, Greece, "OURANOS" Conference Center, on the 10th floor.
New and original research results and the latest state-of-the-art in Attribute-based Credentials and Trustworthiness will be presented by scientific experts and businessmen.
Joint PrimeLife & ABC4Trust Credential Tutorial


Date: June 10th, 2011, from 10:00 to 16:30
Location: IBM Research Zurich, Säumerstrasse 4, 8803 Rüschlikon, Switzerland
Cost: no registration fee
Joint dinner: June 9th, 2011, 19:00 Restaurant Moosegg, Säumerstrasse 31, 8803 Rüschlikon
Trustworthy, yet privacy-preserving authentication is necessary to enable long-term and lifelong privacy for users. Attribute-based credentials offer a solution allowing strong authentication while the user may remain anonymous towards the relying party and without the identity provider learning to know about the websites visited or services deployed by a user. The technology to deploy attribute-based credentials is available with IBM's Identity Mixer and Microsoft's U-Prove. The EC-funded project ABC4Trust now takes up the heritage of the PRIME and PrimeLife projects and will deploy systems using attribute-based credentials in actual production pilots and deliver open reference implementations.






